The Internet and mobile phones have taken over our lives. But it comes with increasing security concerns. Website data breaches, phishing attacks, and other online scams are commonplace.
Here’s a thread for regular people on how to increase your security online, prevent data breaches, phishing attacks, and other online scams, while using your desktop as well as your smartphone.
Revoke App Permissions on Your Google Account
Go to your Google account settings. Revoke permissions from all the apps you don’t use:
https://myaccount.google.com/permissions
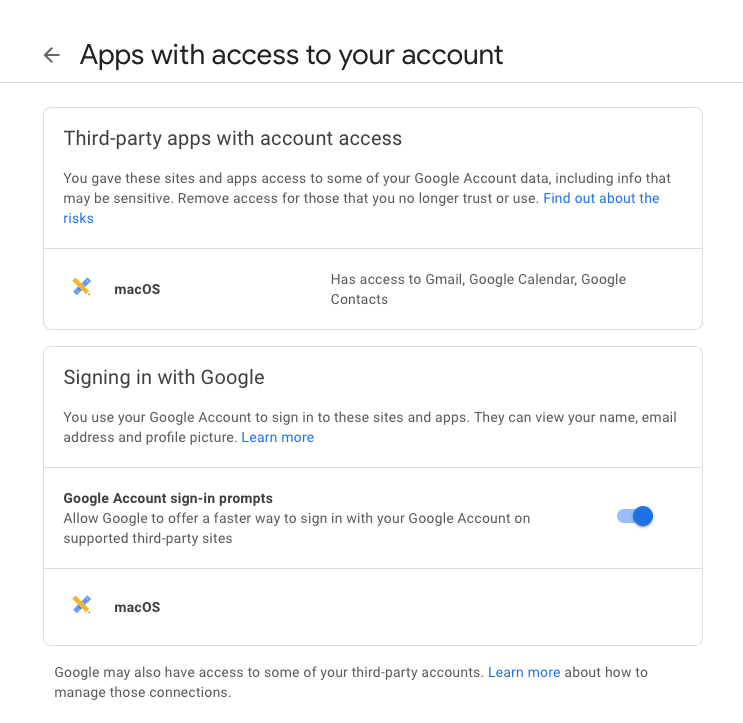
Also, check if any app has access to your contacts or – gasp! – your entire email. Strongly reconsider both, especially access to your email. Giving access to your contacts lets companies spam those people.
Giving access to your email – email organizing apps, for instance – renders your online security meaningless. Password resets are often done with email, and if an external entity can access that, game over!
Revoke App Permissions on Your Twitter Account
Go to your Twitter account settings and revoke permissions from all the apps you don’t use or trust:
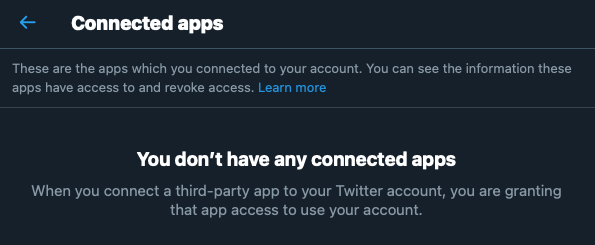
Online quizzes and such sites often ask for permission to post tweets for you, read your tweets, and even your DMs! People click “OK” without reading the fine print.
But imagine the security and privacy risk with having some unknown entity be able to post tweets and read your private DMs just to post the results of what Game of Thrones character you are.
Revoke App Permissions on Your Facebook Account
Go to your Facebook account settings and revoke permissions for all the apps you don’t use:
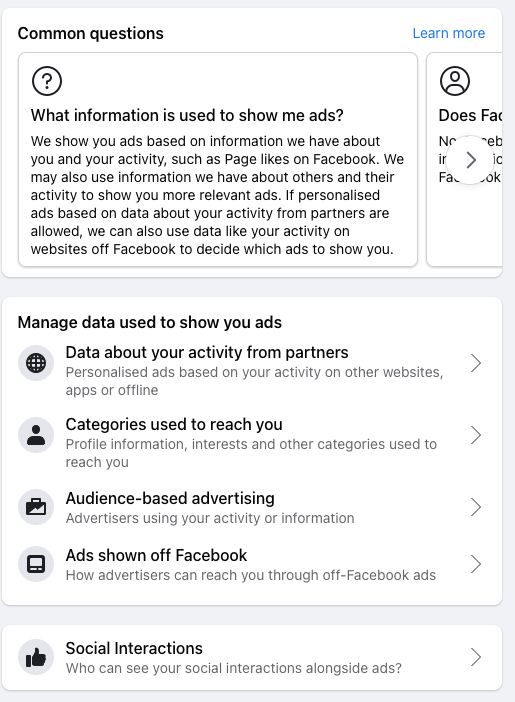
Same reason as for Twitter, but with the added risk that apps have access to vastly more data. There, you might find some app from 5+ years ago that you forgot about.
Remember the Cambridge Analytica scandal? They gained access to lots of data using Facebook quizzes. People gave access to their profiles so they could post answers to dumb quizzes.
In the future, deny access to apps that want to post on social media for you or want access to your contacts. Read the permissions prompts carefully.
NEVER give access to read your email to any app.
If you know what you’re doing, that’s fine.
Use a Password Manager
Always use a password manager to generate random passwords and save them.
Do NOT use the same password for all websites.
Do not use the same password with minor changes like one character modified or a different number added.
Why?
The long version is here:
The only secure password is the one you can’t remember.
Short version: Websites store your passwords, some securely, some less so. Websites also get breached and user data gets leaked. That’s the inescapable nature of technology.
If you use the same password for SiteA as for SiteB, and SiteA gets hacked, your password is now compromised. Somebody could log into SiteB with those credentials.
Random passwords ensure nobody can guess it from your personal info. YsK!4kTu4&$yz8Bz%oq beats John29021980
Which password manager to use?
I use Bit Warden.
While it lacks design polish, it’s free and open source. Has a generator for creating passwords with a shortcut key (I wish I could change it from Ctrl-Shift-9 though.)
Other options are:
KeePassXC
1Password
LastPass
Enable Two-factor Authentication (2FA)
Don’t rely on passwords alone. Whenever possible, enable two-factor authentication (2FA) for every major site like mail, banking, e-commerce, social media, etc. that you use.
This site keeps a list of sites that have 2FA.
The long version of what 2FA is and why you need it: https://authy.com/what-is-2fa/
Short version: it provides extra security in case your password is compromised because somebody guessed it, you wrote it down, or it was found in a data breach of another website.
I use Authy for 2FA.
Other options are:
Google Authenticator
Microsoft Authenticator
TOTP (Time-Based One-time Password) apps work even without an Internet connection. They generate number codes that are valid for a very short time.
Google “how does TOTP work” for fun details.
We digress for a rant: most Indian websites only offer SMS for 2FA. SMS is insecure: it’s plain text, unencrypted, passes through mobile providers, and is vulnerable to SIM swap fraud (google that).
Our websites don’t even offer an option for another method like a TOTP app.
Make Sure Security Questions are Strong Enough
Some sites have “security questions” for verifying accounts. Make sure this isn’t info visible on your social media pages.
“What is your favorite dish?” is not secure if you have a public FB post about how much you love mutton biryani.
Check if You’ve been Pawned
Go check if your account has been compromised in a data breach at haveibeenpwned.com
Register on the site for alerts so you know when a website has leaked your information, and possibly not disclosed it to you like they should have. (Most Indian websites have not.)
Install Software with Verified Safe Source
When installing programs on Windows PC, make sure they’re from a verified safe source and don’t install toolbars or adware. Once an untrusted program is installed on your computer, it could log your keystrokes and it’s game over!
Don’t torrent cracked apps and games.
Download a Malware Scanner
If you’re on a Windows PC, download a malware scanner like Malwarebytes (it’s free) and make sure your system is clean. Their pop-ups to upgrade are damn annoying, but the program is solid.
Get rid of all the shit you find.
Don’t Multiply Security Risks
No matter how much you love or trust your family/partner, don’t share accounts or login info with them. You are multiplying the security risks.
Cliché: chain, the weakest link, etc. All the security tips in this thread are pointless if you have access routes you don’t control.
Google has something called the Inactive Account Manager which allows you to grant access to your account to a trusted person after X days of account inactivity.
Useful for worst-case scenarios. 🤞🏻
How to Boost Your Mobile Security
Everyone has a mobile phone now, and security is often enforced through mobiles. Unfortunately, they can be stolen (easier than computers) or compromised if you don’t change OS defaults. So let’s go.
Enable Screen Lock on Your Smartphone
Make sure your smartphone has auto screen lock enabled after 1-2 minutes of inactivity and needs a password to re-enable. Number and pattern passwords are better than fingerprints and face IDs.
You leave fingerprints all over the place, remember? And people do shit like this. *Oh hello, Aadhaar mafia!*
Google “fingerprint cloning” and be worried.
Disable Message Preview on Your Phone
OTPs sent to mobiles are pointless if other people can see them. Disable displaying SMS and other messages preview on the lock screen. Or you risk a thief seeing your OTP even if your screen is locked.
How?
Android Users: Follow this guide
iOS Users: Follow this guide
Enable Security Verification for Key Apps
For an additional layer of security, enable security verification for key apps like email, social media, and banking.
On Android, you can lock apps using AppLock (download).
OnePlus phones have it built-in.
iOS: https://www.lifewire.com/lock-apps-on-iphone-4164864
Most password reset methods use links sent to your email account. That’s why I keep harping on how important it is to secure your email. Prevent casual access. Lock your phone’s email app.
Your long random password is useless if they can access your email to reset it.
Stop Giving Liberal Permissions to Apps
Be wary of giving liberal permissions to apps, especially for location, storage access, and access to photos and media. Do you want your naughty photos to be visible to every app with access to your media?
Check what permissions your apps have: https://outline.com/wWTruc
Now let’s talk about phishing and social engineering attacks.
These attacks are likely to be far more successful than automated hacking attempts because they prey on human psychological weaknesses.
Impersonating authority figures is an old compliance trick.
Obligatory Wikipedia links: Phishing: https://www.wikiwand.com/en/Phishing
Social engineering: https://www.wikiwand.com/en/Social_engineering_(security)
Please read if you have time. Googling those terms will also give you a lot of info.
Be Very Skeptical about Sharing Info
The most important tip to avoid being phished: let skepticism be your default setting.
Assume calls asking for info about your credit/debit cards aren’t for real. Only give this if *you* call them through a known public contact number.
NEVER Share OTPs or Passwords on Phone
NEVER give OTPs and passwords on the phone, even if Jesus himself calls and asks you.
Too many people have lost money from their accounts via UPI scams because of this. Don’t be the next.
(I’m hoping somebody like @kingslyj has written a thread on how UPI scams work.)
Scammers often impersonate people of authority to use scare tactics into making you give up OTPs for transactions they’ve initiated elsewhere.
Or they use your greed to make your gift/card/prize offers for which they need an OTP.
Don’t fall for any of it.
Don’t Give Up Critical Info for Verification Purposes
Another common scam: impersonating a bank or government officials to make you give up personal and financial information for “verification” purposes. They can then use this information to try hacking your other accounts.
Look before Your Click
Phishing via email is an old scam.
Basic mechanism: a scammer pretends to be a known website, scares you, or tempts you into clicking a link to the website, link goes to another page designed to look like the website but exists so they can capture your username and password.
Next thing you know, your passwords have been changed and you’re locked out while the scammer steals money or orders stuff from your account. Or worse, has access to your email. People get fooled because we’re predisposed to trust known entities that look the part.
NEVER click on a link in an email that leads to a login form. Always type the URL directly. Scammers will set up sites like
XYZlogin.com that looks like XYZ.com but has nothing to do with the original site.
Common types of sites that are impersonated: banks, educational institutions, government sites, social media platforms. Fear and greed are powerful tools.
Common tactics: “security breach, change password ASAP”, “free offer”, “suspicious bank transaction”, “claim your prize”
Even smart and knowledgeable people can fall prey to con artists who dress up a website to look exactly like a trusted site. That’s why I recommend skepticism as the default position.
Email headers too can be easily spoofed to look like they’re from a legit source. These emails can then link to scam sites.
We tend to think that if something comes from a domain like somebankofficial.com, it’s a legit email from somebank.com
Do NOT assume this.
Wrapping up, some final thoughts:
- Data protection in India is a joke. Lots of e-comm sites have had breaches. Somebody knowing stuff about you doesn’t make them reliable.
- This is a thread meant for the average person to be wary, not a comprehensive security tutorial. 🙂
- Don’t trust; verify
- More determined attackers who specifically target you (especially if you’re a public figure) may have more resources to try fooling you. The more popular you are, the more cautious you should be.
- Security and convenience/usability are often trade-offs.
- Governments can probably use coercion to make entities give up info about you without your knowledge.
- Stuff you put on the Internet is only as secure as the security of the recipient or platform it’s posted on. Once you send something, it’s out of your hands.
Disclaimer: This post first appeared here.
